Your Personal Data Was Potentially Exposed by a Flaw in 140+ Airlines' Software
Most travelers know not to share un-masked photos their boarding passes online. By scanning the barcode or just reading the name and reservation number off the boarding pass, anyone can access your personal data and may be able to change or cancel your flight. However, until last week, hackers didn't need your boarding pass to get your data or wreak havoc on your reservation if it was booked through one of more than 140 airlines.
While the average flyer probably has not heard of Amadeus or Sabre, most airlines across the world use one of these two major reservation systems. And Israeli hacker Noam Rotem -- working with Safety Detective -- discovered a major flaw in Amadeus that left a backdoor open for hackers to easily access passengers' data, including birthday, address, email, phone number and access to frequent flyer accounts.
Chances are you've booked a flight through one of the airlines that uses the Amadeus reservation system. These airlines include: Air Canada, Air France, ANA, Asiana, Austrian, British Airways, Brussels Airlines, Cathay Pacific, El Al, EVA Airways, Finnair, Iberia, Icelandair, KLM, Korean Airways, Lufthansa, Malaysian Airlines, OpenSkies, Qantas, SAS, Singapore Airlines, SWISS, TAP Portugal, Thai Airways and many more.
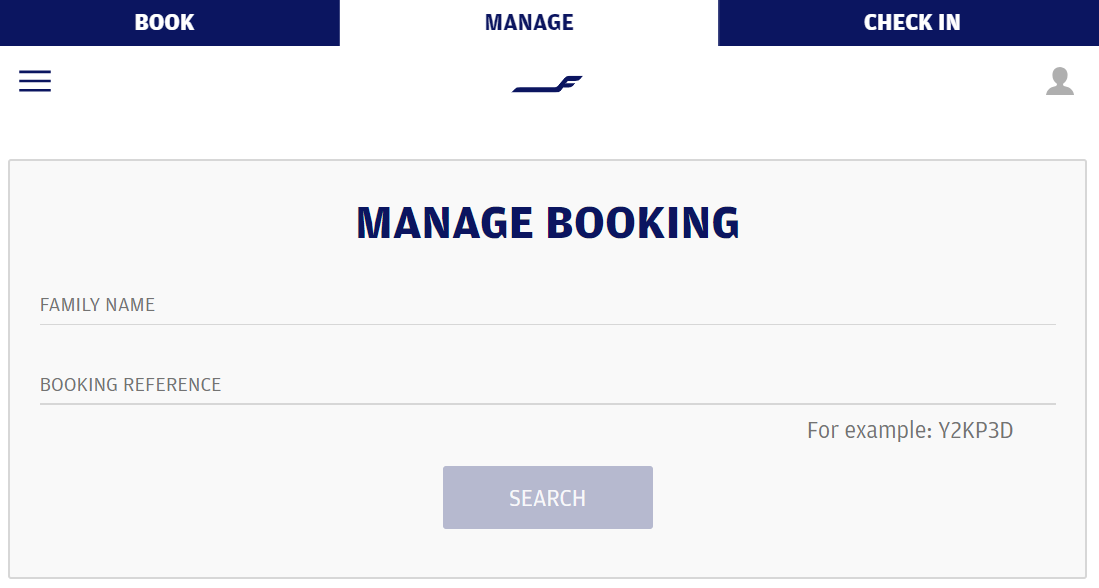
Even without this flaw, it doesn't take much to access an airline reservation. Typically, all you need is the last name of the passenger and the Personal Name Record (PNR) for the reservation. However, using El Al's reservation system, researchers found that they could simply tweak a URL to pull up any Amadeus reservation using just the six-digit Personal Name Record (PNR). The passenger's last name wasn't required.
Even worse, the researchers found that there was no limitation in place to keep them from randomly generating numbers and pinging the Amadeus system to check if there was an active reservation using that PNR. While there are around two million possible six-digit alphanumeric combinations, the researchers were able to go through possibilities with decent speed:
Through this process they were able to retrieve an undisclosed number of active reservations. And once they found a match, the researchers report:
"We were able to log into El Al's customer portal and make changes, claim frequent flyer miles to a personal account, assign seats and meals, and update the customer's email and phone number, which could then be used to cancel/change flight reservation via customer service."
Being "white-hat hackers," the researches shared their discovery with Amadeus -- along with suggestions to add reservation passwords, captcha and other "bot protection mechanisms" to keep this from being possible in the future.
Amadeus responded to Safety Detective that it "took immediate action" to fix the issue and "can now confirm that the issue is solved."
"To further strengthen security, we have added a Recovery PTR to prevent a malicious user from accessing travelers' personal information, the company's statement continued. "We regret any inconvenience this situation might have caused."

As this wasn't a traditional hack -- like Marriott, Cathay Pacific, Equifax and more -- its unclear how many passengers' data may have been exposed through this simple reservation access method. Amadeus says it hasn't detected a data breach.
"We became alerted to an issue in one of our products and our technical teams took immediate action and as of January 16 the issue was fixed," Amadeus said in a statement to TPG. "We can confirm that Amadeus has not detected any data breach and that no data from travelers was disclosed. We regret any disruption this situation may have caused."
However, it seems it would be tough for Amadeus to be sure that "no data from travelers was disclosed." It's possible that Amadeus could see from its logs whether another brute-force attack -- similar to the one that the researchers used -- had been employed. However, this reservation access method is identical to how El Al passengers would access their reservations when clicking through a confirmation email. Indeed, that's how the hacker discovered this access method. So, at the very least, it would likely be difficult to say for sure that bad actors didn't utilize this reservation access method on a smaller scale.
Looking forward, there clearly needs to be a better way to secure flight reservation data than the archaic procedure that simply requires a PNR and the traveler's last name. In its statement, Amadeus emphasizes that it realizes this and is working "together with our customers and partners in the industry to address PNR security overall."
"The airline industry relies on IATA standards that were introduced to improve efficiency and customer service on a global scale," the company said. "Because the industry works on common industry standards, including the PNR, further improvements should include reviewing and changing some of the industry standards themselves, which will require industry collaboration."
Speaking of the International Air Transportation Association (IATA), the standard-setting industry group finally released a statement on Wednesday -- almost a week after the disclosure about the backdoor. The statement pledges that "IATA is committed to working with industry stakeholders to ensure passenger information remains secure."
The Department of Transportation and Federal Aviation Administration were unable to be reached for comment due to the partial government shutdown.
TPG featured card
at American Express's secure site
Terms & restrictions apply. See rates & fees.
| 4X | Earn 4X Membership Rewards® points per dollar spent on purchases at restaurants worldwide, on up to $50,000 in purchases per calendar year, then 1X points for the rest of the year. |
| 4X | Earn 4X Membership Rewards® points per dollar spent at US supermarkets, on up to $25,000 in purchases per calendar year, then 1X points for the rest of the year. |
| 5X | New! Earn 5X Membership Rewards® points on prepaid hotel stays booked through AmexTravel.com or the Amex Travel App. |
| 3X | Earn 3X Membership Rewards® points on flights booked through AmexTravel.com, the Amex Travel App, or purchased directly from airlines. |
| 2X | Earn 2X Membership Rewards® points on prepaid car rentals booked through AmexTravel.com or the Amex Travel App and cruises booked and paid through AmexTravel.com. |
| 1X | Earn 1X Membership Rewards® point per dollar spent on all other eligible purchases. |
Pros
- Valuable dining and food-related credits
- Flexible rewards with airline and hotel transfer partners
- Multiple travel and purchase protections
- No foreign transaction fees
- Access to Amex Offers for additional savings (enrollment required)
Cons
- Not as useful for those living outside the U.S.
- Some may have trouble using Uber and other dining credits
- You may be eligible for as high as 100,000 Membership Rewards® Points after you spend $8,000 in eligible purchases on your new Card in your first 6 months of Card Membership. Welcome offers vary and you may not be eligible for an offer. Apply to know if you’re approved and find out your exact welcome offer amount – all with no credit score impact. If you’re approved and choose to accept the Card, your score may be impacted.
- Earn 4X Membership Rewards® points per dollar spent on purchases at restaurants worldwide, on up to $50,000 in purchases per calendar year, then 1X points for the rest of the year.
- Earn 4X Membership Rewards® points per dollar spent at US supermarkets, on up to $25,000 in purchases per calendar year, then 1X points for the rest of the year.
- New! Earn 5X Membership Rewards® points on prepaid hotel stays booked through AmexTravel.com or the Amex Travel App.
- Earn 3X Membership Rewards® points on flights booked through AmexTravel.com, the Amex Travel App, or purchased directly from airlines.
- Earn 2X Membership Rewards® points on prepaid car rentals booked through AmexTravel.com or the Amex Travel App and cruises booked and paid through AmexTravel.com.
- Earn 1X Membership Rewards® point per dollar spent on all other eligible purchases.
- Pay It® lets you tap in the American Express® App to quickly pay for small purchase amounts throughout the month and still earn rewards the way you usually do. Plan It® gives you the option to split up big purchases into equal monthly payments with a fixed fee. You’ll know upfront exactly how much you’ll pay.
- Updated! $120 Dining Credit: Earn up to a total of $10 in statement credits monthly when you pay with the Gold Card at Grubhub (including Seamless), Buffalo Wild Wings, Five Guys, The Cheesecake Factory, and Wonder. This can be an annual savings of up to $120. Enrollment required.
- $100 Resy Credit: Get up to $100 in statement credits each calendar year at over 10,000 qualifying U.S. Resy restaurants after you pay for eligible purchases with the American Express® Gold Card. That’s up to $50 in statement credits semi-annually. Enrollment required.
- $84 Dunkin' Credit: Earn up to $7 in monthly statement credits after you pay with the American Express® Gold Card at U.S. Dunkin’ locations. Enrollment required.
- $120 Uber Cash on Gold: Enjoy up to $120 in Uber Cash annually with your Gold Card. Just add your Card to your Uber account and you'll get $10 in Uber Cash each month to use on orders and rides in the U.S. when you select an Amex Card for your transaction.
- New! As an American Express® Gold Card Member, you can enjoy complimentary Hertz Five Star® Status. Enjoy benefits like skipping the counter at select locations, adding an additional driver at no additional cost*, and vehicle upgrades**. Benefit enrollment and Hertz Gold+ registration are required. *Additional drivers must meet standard rental qualifications and must be a spouse or domestic partner to qualify as complimentary. Other additional drivers subject to fees. **Benefits are subject to availability and vary by location. Additional Hertz program Terms and Conditions including age restrictions apply.
- Take advantage of a $100 credit towards eligible charges* at over 1,300 upscale hotels worldwide when you book The Hotel Collection through AmexTravel.com or the Amex Travel App **. *Eligible charges vary by property. **The Hotel Collection requires a two-night minimum stay.
- Book your travel through the Amex Travel App with added peace of mind – backed by American Express® service and support. Only for American Express® Card Members.
- Whenever you need us, we're here. Our Member Services team will ensure you are taken care of. From lost Card replacement to statement questions, we are available to help 24/7.
- No Foreign Transaction Fees.
- Annual Fee is $325.
- Terms Apply.


